Hello everyone,
A couple of days ago, I had the opportunity to join a little CTF event (RootersCTF) with some friends, let’s start this blog with some code reversing. 🙂
The CTF we are going to work on today is titled RootersCTF – CH04 held on 2019, along with other categories (web apps, forensics, cryptography, etc..).
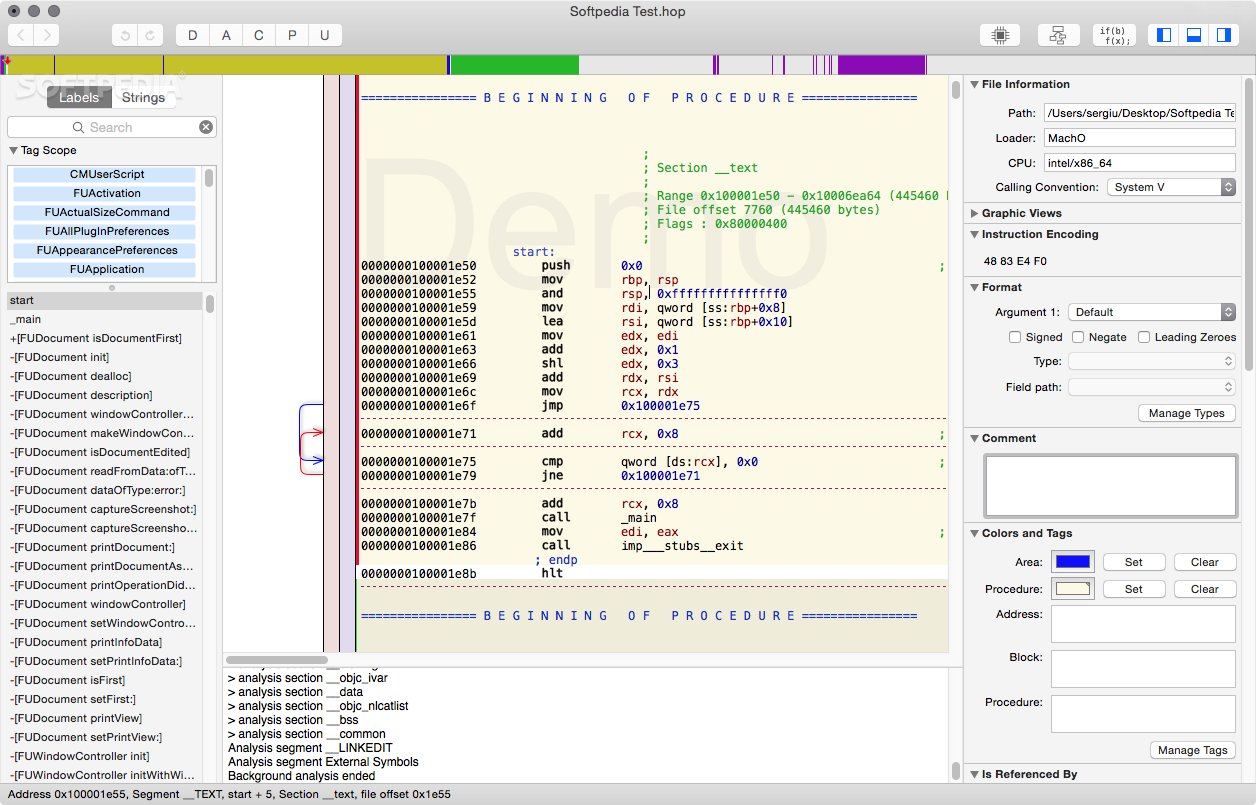
As we can see from the CH04’s prompt on the CTF website, or using file Linux utility, we can see that this is an ELF binary with its section header stripped, so we won’t be able to execute the binary for now, which means the only option we currently have is static analysis. (alternative approach would be to learn about the ELF File Format, and try to repair the section header manually, however that’s overkill)
Let’s start by loading our ELF binary into IDA Free disassembler, the first thing we can notice in the binary is long initializations of bytes.
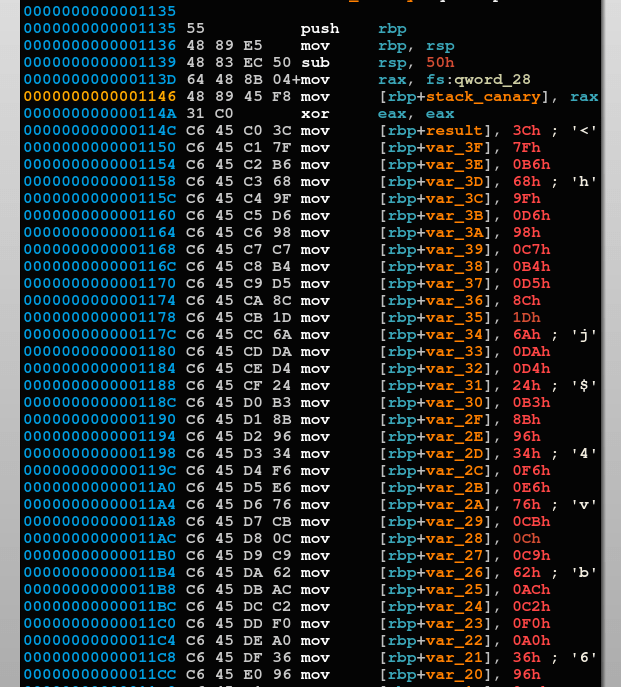
For now, let’s keep analyzing what the function is doing after all the initialization instructions.
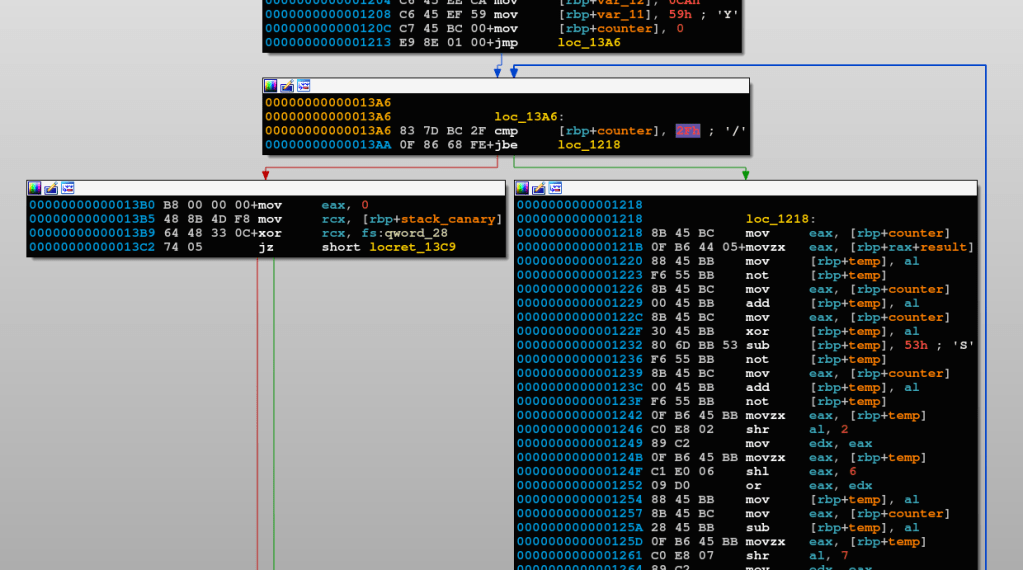
It seems to be doing a long set of arithmetic and bitwise operations on the previously initialized bytes, within a loop that iterates 47 times.
I’m a high fan of manual decompilation, in my opinion it’s the only way you can truly learn Reverse Code Engineering, automatic decompilers sometimes tend to contain false positives and wrong translations.
So, after decompiling the instructions starting at loc_1218, here is the C++ decompiled equivalent.
#include <iostream>
using namespace std;
unsigned char encPayload[] = {
0x3C,0x7F,0xB6,0x68,0x9F,0xD6,0x98,0xC7,
0xB4,0xD5,0x8C,0x1D,0x6A,0xDA,0xD4,0x24,
0xB3,0x8B,0x96,0x34,0xF6,0xE6,0x76,0xCB,
0x0C,0xC9,0x62,0xAC,0xC2,0xF0,0xA0,0x36,
0x96,0xBF,0x76,0x5A,0xBB,0x76,0x0E,0x92,
0x3B,0x29,0x4A,0x55,0xE6,0xEE,0xCA,0x59
};
int main(){
unsigned char decPayload[sizeof(encPayload)+1] = {};
unsigned char temp, temp2, temp3, counter;
temp = 0;
temp2 = 0;
temp3 = 0;
counter = 0;
while (counter <= 47){
temp = encPayload[counter];
temp = ~temp;
temp += counter;
temp ^= counter;
temp -= 0x53;
temp = ~temp;
temp += counter;
temp = ~temp;
temp2 = temp >> 2;
temp3 = temp << 6;
temp3 |= temp2;
temp = temp3 & 0xFF;
temp -= counter;
temp2 = temp >> 7;
temp3 = temp + temp;
temp = temp3 | temp2;
temp ^= counter;
temp += 0x21;
temp ^= counter;
temp2 = temp >> 1;
temp3 = temp << 7;
temp = temp3 | temp2;
temp -= counter;
temp ^= counter;
temp -= counter;
temp = -temp;
temp -= counter;
temp2 = temp >> 1;
temp3 = temp << 7;
temp = temp3 | temp2;
temp ^= 0x84;
temp2 = temp >> 2;
temp3 = temp << 6;
temp = temp3 | temp2;
temp ^= 0xBD;
temp2 = temp >> 5;
temp3 = temp << 3;
temp = temp3 | temp2;
temp -= 0x7F;
temp = ~temp;
temp += counter;
temp = ~temp;
temp += 0x7C;
temp ^= 0xC9;
temp = ~temp;
temp -= 0x37;
temp = ~temp;
temp = -temp;
temp2 = temp >> 5;
temp3 = temp << 3;
temp = temp3 | temp2;
temp -=counter;
temp ^= counter;
temp += counter;
temp = -temp;
temp = ~temp;
temp -= 0x7D;
temp ^= counter;
temp -= 0x1E;
temp ^= 0x1E;
temp -= 4;
temp2 = temp >> 6;
temp3 = temp << 2;
temp = temp3 | temp2;
temp ^= counter;
temp += counter;
temp2 = temp >> 2;
temp3 = temp << 6;
temp = temp2 | temp3;
temp = ~temp;
decPayload[counter] = temp;
counter++;
}
for(int i = 0; i < sizeof(decPayload); i++)
cout << decPayload[i] << flush;
cout << endl;
return 0;
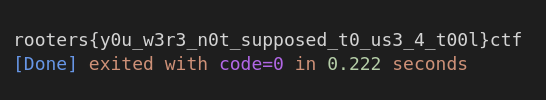
}Compiling and running this program, we get the flag!