Hello everyone,
So here is CH02 reversing challenge from RootersCTF.
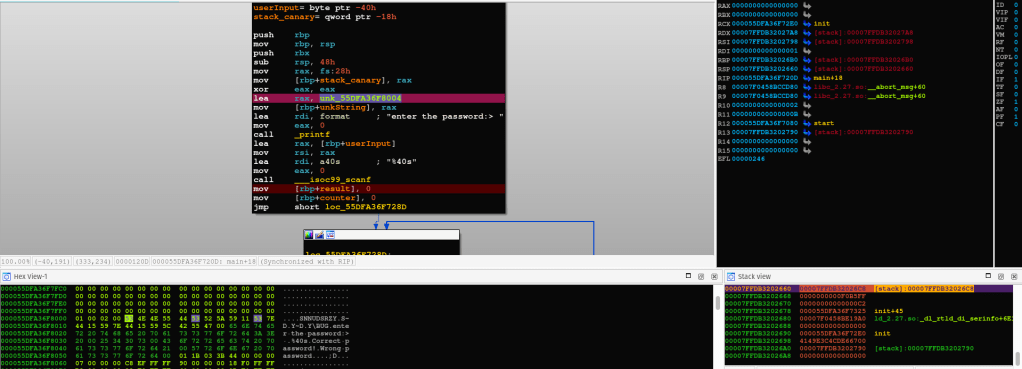
This is a pretty straightforward challenge, as soon as we load it into IDA Free disassembler, we can see the following simple logic.
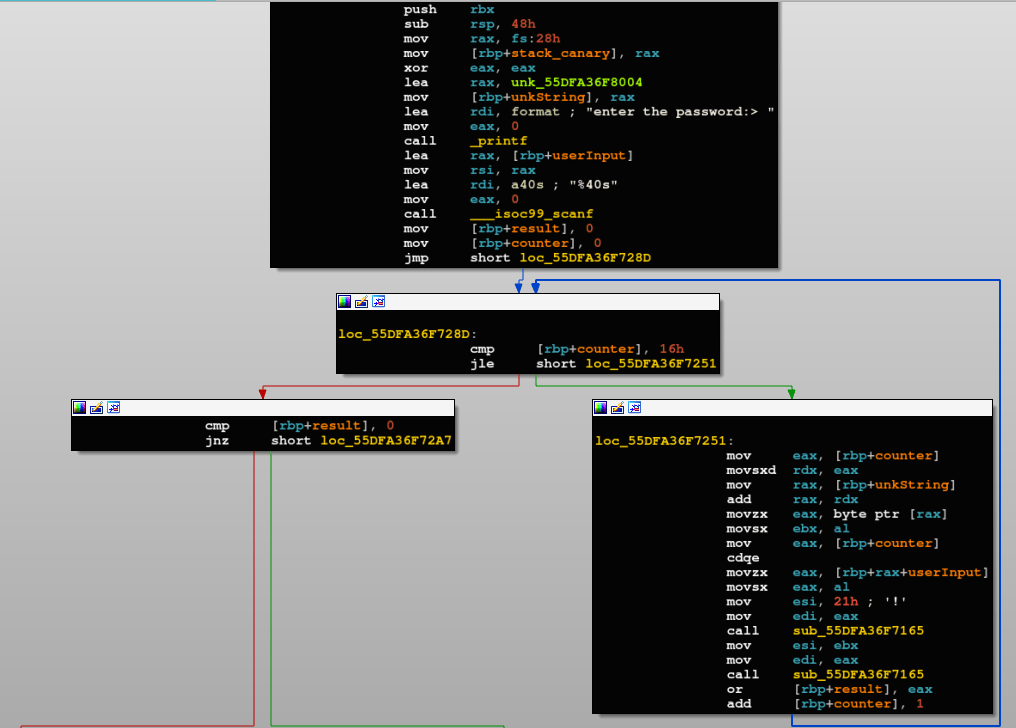
First an unknown memory address is copied in a variable (denoted in the screenshot by unkString), the program starts by taking the user’s input, then applies couple of operations on it, and based on the results it either displays Correct Password or Wrong Password message to the user.
In these types of challenges, and for the sake of time, I usually start by investigating the unknown sequence of bytes, why you may ask? Sometimes, those bytes could be simply analyzed and decrypted/decoded without even looking at what the program does on them, if that’s the case, the challenge usually shouldn’t take more than 10 minutes until you submit the flag on the website. 😉
Let us have a look at the bytes in memory.
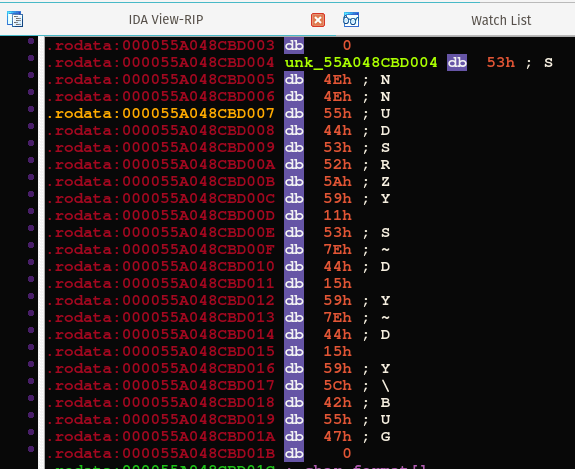
We already know that the flag format is: rooters{%s}, and the shown unknown bytes start with \x53\x4E\x4E\x55, the second and third bytes are identical, similar to the flag.
The simplest encryption used in a lot of CTF’s is XOR encryption, let’s check it out, but first we need to know the key against which each of the given bytes will be XOR’ed. We already think that \x4E is the encrypted byte for character 'o', which has the ASCII value of \x6f, XOR’ing those values together gives \x21.
Using a few IDC lines, let’s check if our guess was correct.
extern srcAdd, BuffSize;
srcAdd = 0x55A048CBD004;
BuffSize = srcAdd + 24;
for(srcAdd = srcAdd; srcAdd < BuffSize; srcAdd = srcAdd + 1) {
patch_byte(srcAdd, get_db_byte(srcAdd)^0x21);
}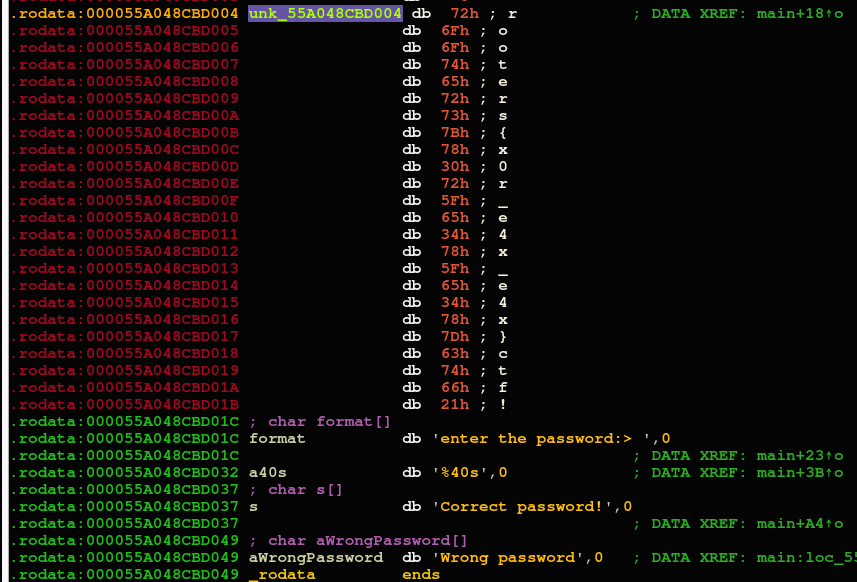
Great, the flag is rooters{x0r_e4x_e4x}ctf.