Hello everyone,
In this post, we are going to solve the CH03 challenge in the RootersCTF 2019. As CH02, this is going to be pretty straightforward, so I won’t be getting into much details.
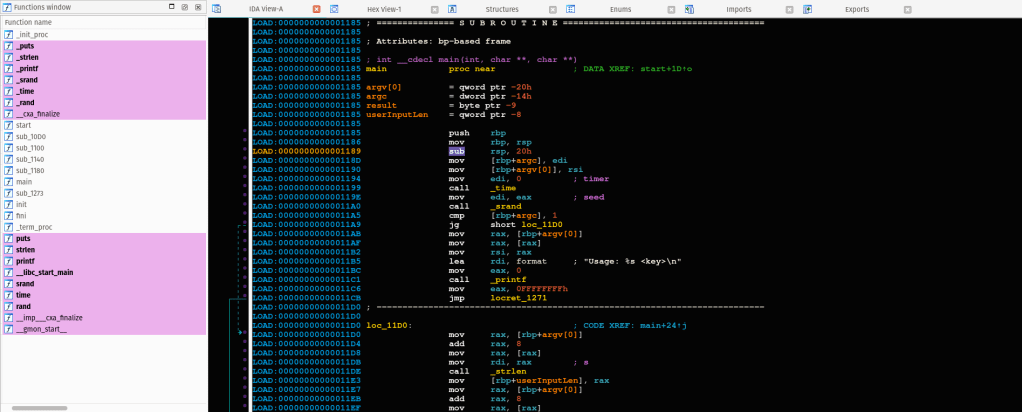
As soon as we load the binary file into IDA, we can see it simply takes the first command line argument argv[1], stores the length into a variable, and calls sub_1273 with the length and the given user input as parameters.
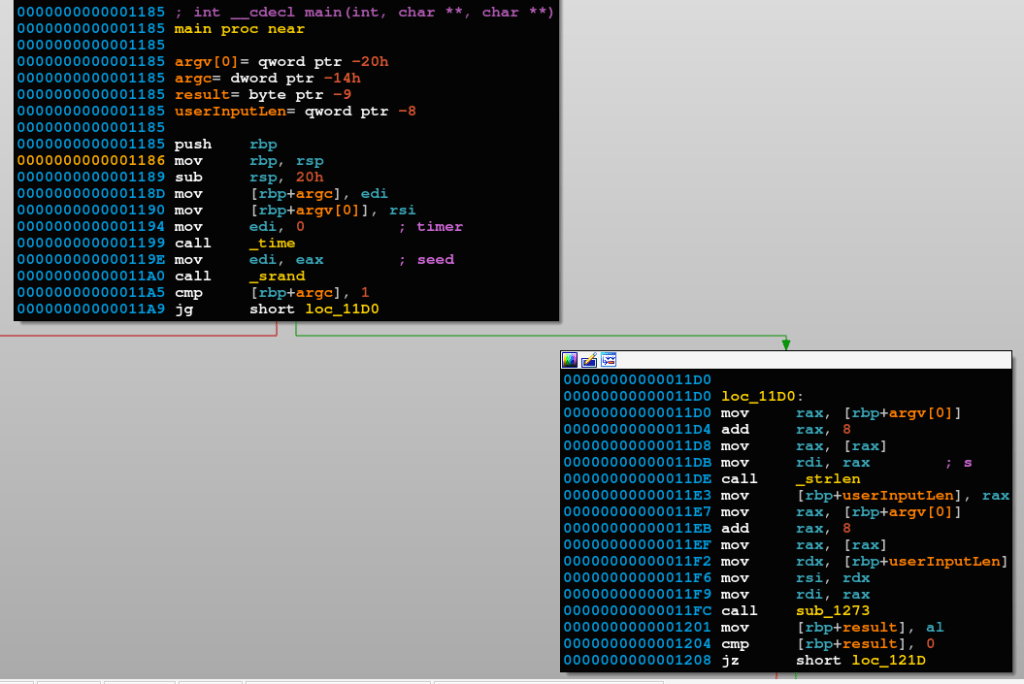
Stepping into sub_1273.
As in CH02 challenge, we can see there is a reference to an unknown sequence of bytes in memory at offset 0x43E0.
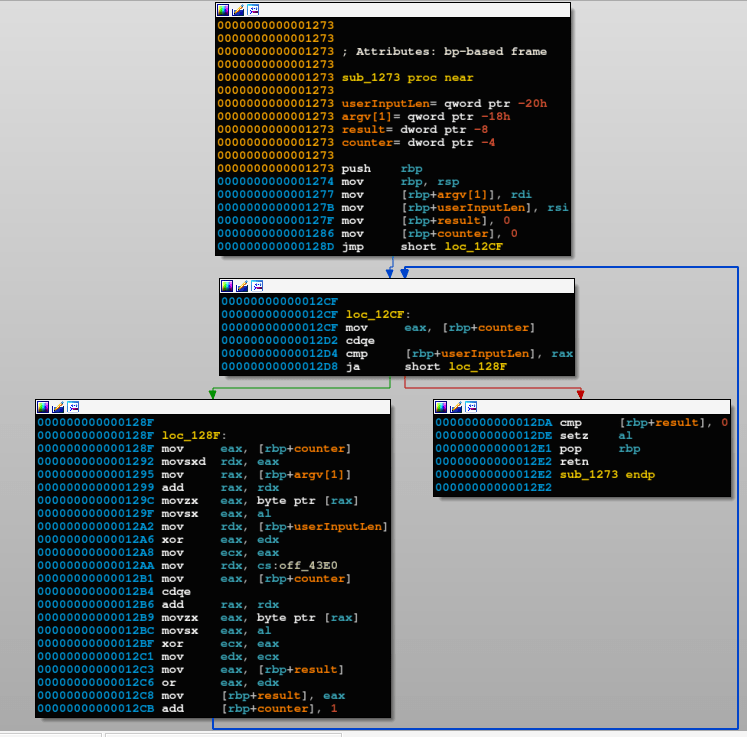
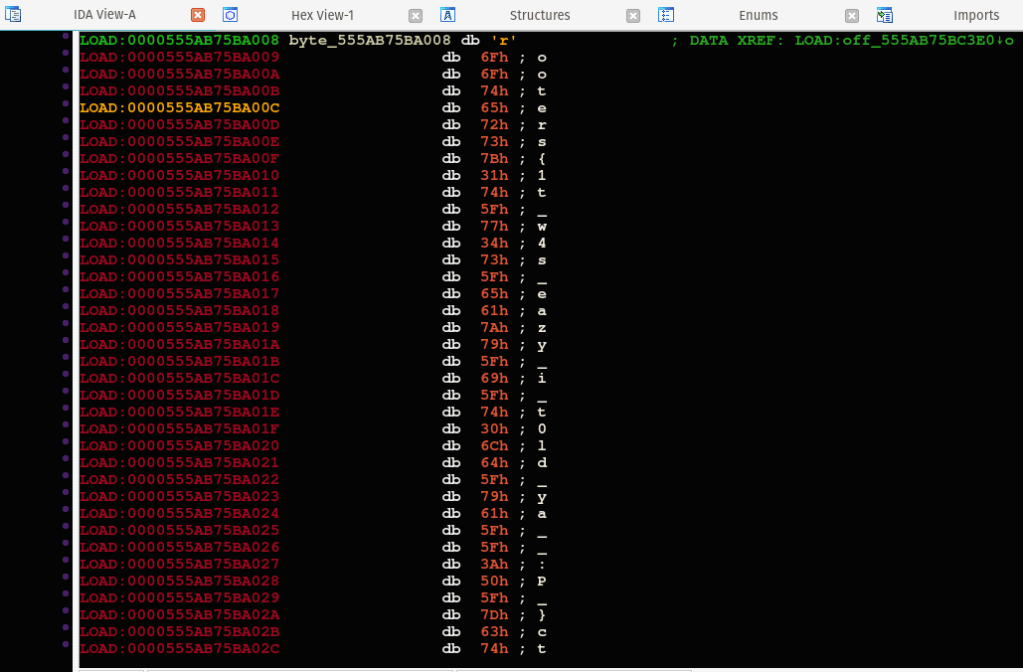
Let us dump the bytes in there.
As we did in the previous article (CH02 writeup), let’s have a look at the given sequence of bytes. As shown in the above screenshot, the sequence starts with \x54\x49\x49\x52. Again, that looks familiar, the flag format is rooters{%s}ctf, XOR’ing 0x49 against 0x6f the ASCII value of character 'o', we get what we think is the key for the XOR’ing encryption scheme0x26.
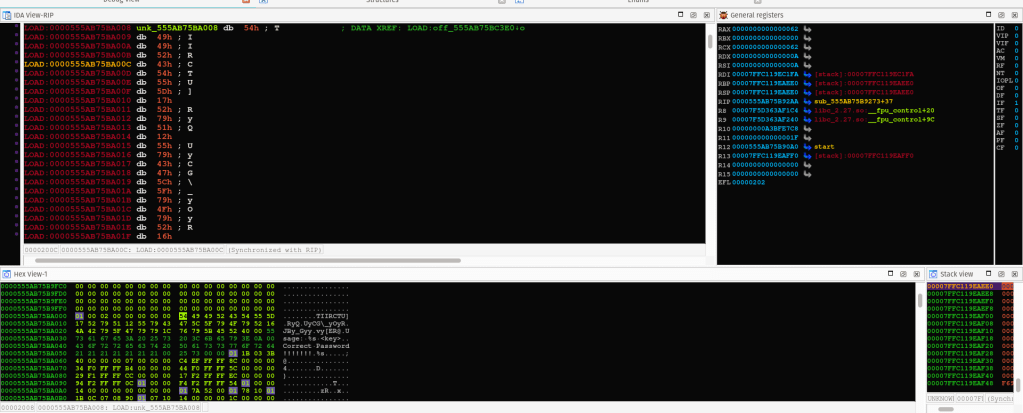
Let’s write an IDC line that decrypts the bytes for us and check the results.
extern srcAdd, buffSize;
srcAdd = 0x555AB75BA008;
buffSize = srcAdd + 50;
for(srcAdd = srcAdd; srcAdd < buffSize; srcAdd = srcAdd + 1) {
patch_byte(srcAdd, get_db_byte(srcAdd)^0x26);
}
As expected, a single-byte XOR encryption algorithm was the one used to encrypt the flag.
The flag is: rooters{1t_w4s_eazy_i_t0ld_ya__:P_}ctf